- How to setup SSH – Install SSH server and client
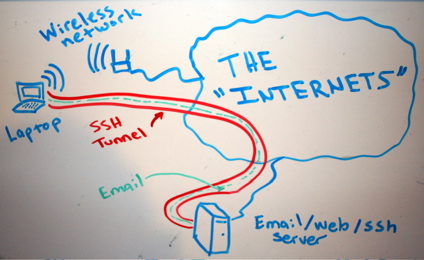
- SSH as SOCKs 5 proxy
- Linux user account with ssh-only permissions
SSH (among other things) is a secure way of proxy-ing your traffic, web browsing or accessing a service remotely which is blocked by a firewall. In case we want someone else to have that access or securely proxying his traffic etc etc, we need to provide a user account with ssh-only access to our ssh server… Well, the solution described below is not best practice but it’s secure and fast to implement.
- Create a user, set the home folder, set preferred shell (rbash or nologin if you want your user use keys and not password).
- Give it a password
- Append at the end of the .profile file an empty variable PATH, so even if the user log in he can’t do anything else than… just log in!
- Remove write permissions from home directory.
- Remove write permissions form .bash_logout, .profile and .bashrc
|
1 2 3 4 5 6 7 8 9 10 11 |
useradd sshtunnel -m -d /home/nameoftheuser -s /bin/rbash passwd sshtunnel echo "PATH=\"\"" >> /home/nameoftheuser/.profile chmod 555 /home/nameoftheuser/ cd /home/nameoftheuser/ chmod 444 .bash_logout .bashrc .profile |